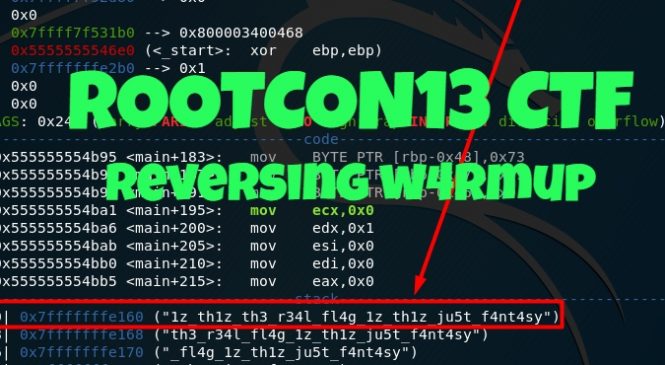
ROOTCON13 CTF – Reverse Engineering – W4RMUP
It’s the time of the year when ROOTCON, the largest security conference in the Philippines, is back in action. This was my 2nd time attending the conference and my 2nd time joining ROOTCON’s Capture the Flag event. Last year’s CTF was a close game since AJ, Ameer, and I placed 2nd from the overall score but we were able to pull off the 1st place this year against other strong teams including our hackstreetboys teammates Ariz, Felix, and Jym from [hsb]JumboHackdog, and IJ from DiKoPoAlam.
It was honestly a challenging game thanks to the awesome guys from Pwn De Manila.
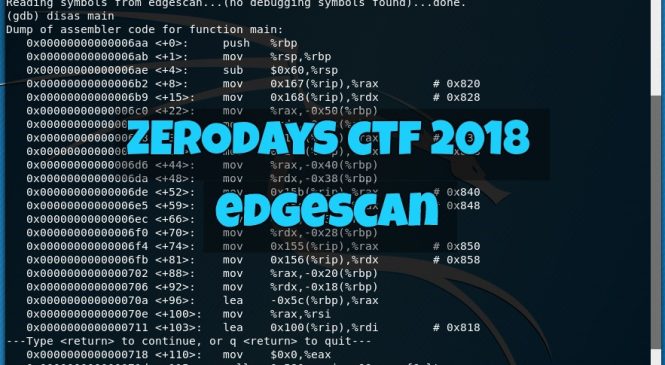
Since AJ and Ameer did the web (nearly a board wipe!) which can be seen here, I was doing other categories and gonna share this reverse engineering challenge that I managed to solve during the event.
This